NELLIS AIR FORCE BASE, Nev. (AFNS) -- On Jan. 11, the Air Force concluded the first department-wide, secret classification innovation hackathon at Nellis Air Force Base inside the Threat Training Center’s hangar following six days of 24-hour operations.
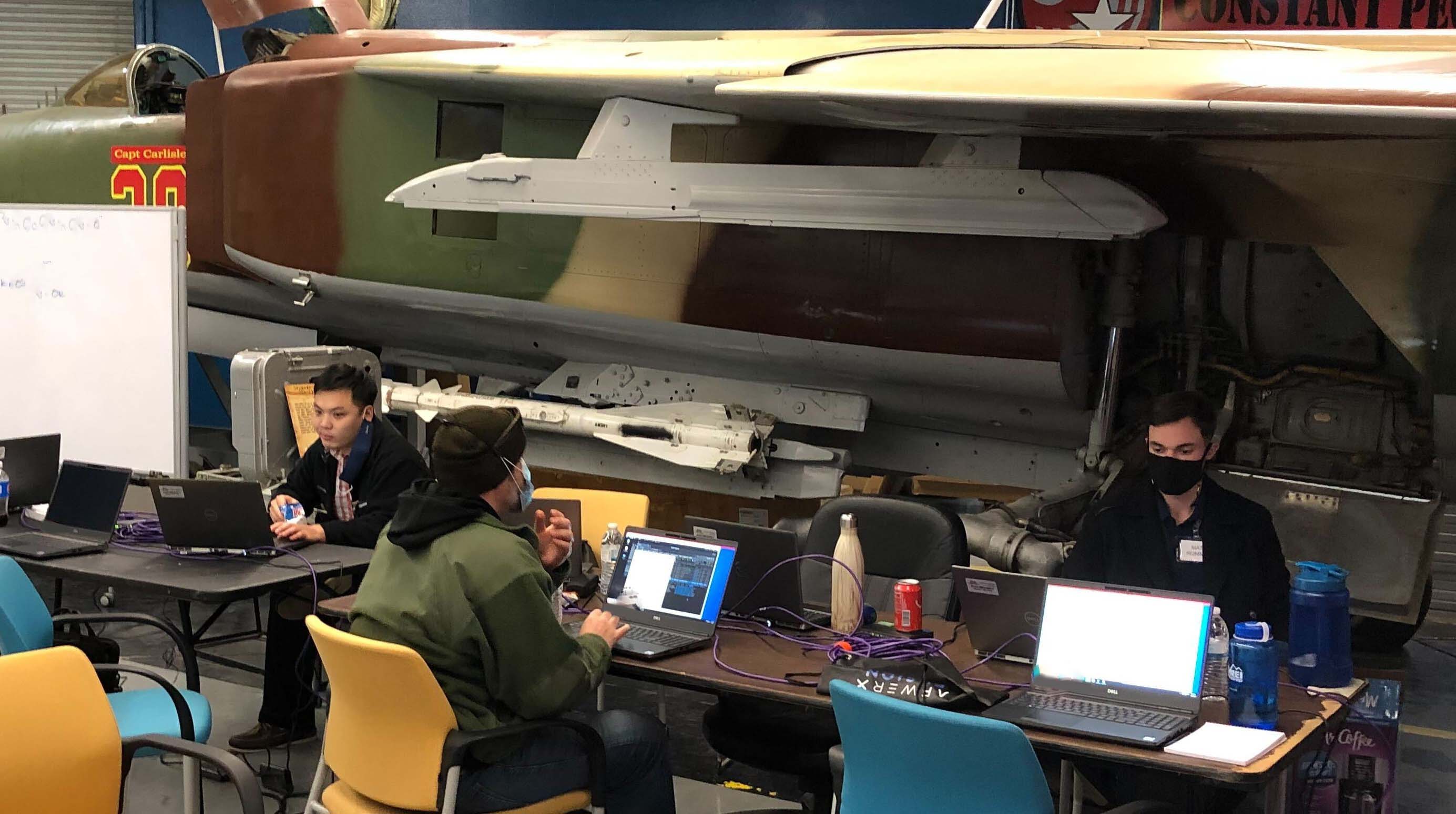
Working beneath the wings of MiG jets strewn with duct-taped network and power cables, over 80 hackers – product managers, engineers, pilots, and data and visualization scientists – of experience ranging from E-3 to general officer and with contributions from 12 industry partners – developed capabilities leveraging Air Force weapons, sensor, health and maintenance data. These new capabilities were demonstrated during a science fair-style exhibition.
The approximately 200 hackers, support staff, attendees and judges came from Air Force software engineering groups, software factories, and flight and frontline units. The group included 15 general officer-level attendees and judges including the Air Force’s vice chief of staff, chief data officer, chief experience officer, chief science officer, and additional senior members from Air Combat Command.
Stuart Wagner, the Department of the Air Force’s chief digital transformation officer, set the original vision for the event.
“Universities and technology companies have sponsored hackathons for decades where attendees rapidly develop products leveraging data and technology infrastructure,” Wagner said. “We believed a classified-level hackathon could develop emergent weapons system capabilities at unprecedented speed and consequence and at lower cost. Senior leaders have validated this hypothesis.”
The event’s 11 teams focused on challenges such as: jet sensor visualization and playback, target planning and pairing, multi-jet sensor fusion analysis, artificial intelligence-assisted radar sensor failure mitigation, maintenance visualization and automation/artificial intelligence-assisted personnel recovery.
“DoD has prioritized security to such an extreme that it has hindered our ability to adapt weapons systems to emerging threats. Adversaries regularly release unseen capabilities demanding agility,” Wagner said. “If we build and refine capabilities and tactics in an integrated manner against daily collected telemetry data, we can deploy these updates improving our ability to react and deter new red capabilities. By taking a risk-on approach to need to know, software availability and data accessibility with appropriate controls, BRAVO hackathons will change how we enact warfare.”
Teams brought in open-source software, built their own virtual machine images and added live data such as new automatic dependent surveillance-broadcast recordings.
The BRAVO hackathon’s “maiden voyage” included support from Air Force CyberWorx, Chief Information Office, Chief Data Office, ACC (Operations, 350th Spectrum Warfare Wing, Chief Scientist Officer, 59th Test and Evaluation Squadron, Shoc-N), 16th Air Force, Morpheus, AFWERX, TRON, Joint Artificial Intelligence Center, and others.
The event included industry involved through the Air Force CyberWorx Partnership Intermediary, which selected 12 industry partners from a pool of about 60 applicants.
Lt. Col. Judson Dressler, CyberWorx director, noted, “Industry partners played a critical role at BRAVO, and CyberWorx will be considering more ways to break down barriers between industry and government.”
This year, BRAVO expects to scale up to exercises involving more than 500 inter-service, inter-agency, foreign partner, and industry hackers.
While hackathon events are sometimes mistakenly identified as solely security-focused, the Air Force plans to use these events to creatively improvise or “hack” solutions to unsolved problems or limitations.
Outputs from these events range from an immediate capability for operational integrators to idea prototypes that support questions asked from program offices, requirements officers, or strategic offices. Led by Jimmy Jones, the STITCHES Warfighter Application Team, which hosted the information system for the event, is leading post-hackathon operationalization.
To allow hackers to quickly develop software and AI capabilities, BRAVO utilized the Joint AI Center’s Joint Common Foundation platform led by Capt. T.J. Wiley, AI Infrastructure and Platforms chief at the Joint Artificial Intelligence Center.
"Through our partnership with the Air Force, we delivered our newest enterprise-level AI DevSecOps capability to the event while obtaining important feedback from a diverse group of data scientists and developers solving real-world problems,” Wiley said.
Named BRAVO in the spirit of Project B, attendees wore shirts emblazoned with messages such as: “Build >> Talk,” “Be Disagreeable,” and “#3.” The event provided a new level of creative freedom to hackers who pitched ideas, formed teams, and even selected their working hours.
The BRAVO hackathon series is named from Project B, a 1921 series of joint Army-Navy target exercises conducted on surplus ships in response to Army Brig. Gen. Billy Mitchell’s claim that bombers sink battleships. This claim undermined the then-current investments and strategy of the then Department of War. SECWAR and SECNAV authorized Project B to disprove and disgrace Mitchell by demonstrating the insignificance of airpower. Mitchell instead directed his bombers to destroy all the test ships, changing military strategy, defense resourcing for aeronautics and aircraft carriers, and ultimately the Department of War by proving the need for a separate Air Force military department.
Styled off Project B, BRAVO hackathons are sponsored by senior Department of Defense leaders to provide technical and cultural innovation environments that enable government and industry to test and validate bold ideas on real Department of Defense data.